Cyber defense is still often treated as an abstract function, concentrated in specialized hubs and managed at a distance from operations. That view, however, is becoming increasingly incomplete.
The delivery of the first defensive kits to the United States cyber command marks a tangible shift. For the first time, standardized, transportable equipment is being positioned for direct use on partner networks, signaling a clear effort to bring cyber capabilities closer to field operations.
At the same time, public cybersecurity agencies are increasingly treating space systems as critical infrastructure exposed to cyber threats, highlighting the extent to which digital capabilities now depend on distributed physical architectures.
Taken together, these developments point to a deeper shift. Cyber defense is no longer just an institutional function. It is becoming a deployable capability, shaped by operational constraints and dependent on the environments in which it operates.
A global landscape that is evolving unevenly
Globally, this shift is unfolding unevenly. Some states continue to rely on centralized models built around national capabilities and specialized organizations. Others are moving toward approaches more tightly integrated with military operations.
The United States currently stands at the forefront of this evolution, particularly through its forward presence operations on partner networks. These missions, conducted at the invitation of allied states, aim to detect malicious activity directly within foreign infrastructures before it can spread further.
At the same time, European institutions are increasingly incorporating the space dimension into their assessment of cyber risk. Satellite systems are now widely recognized as critical dependencies for digital operations, rather than as peripheral enablers. The landscape remains fragmented, but the direction is clear. Cyber can no longer be understood in isolation from the physical and technical environments that support it.
United States deployable kits make the shift visible
The emergence of standardized defensive cyber kits does not represent a sudden break. It makes visible a transformation that has been underway for several years.
These kits are designed for rapid deployment, including in partner environments, allowing specialized teams to detect, analyze, and understand malicious activity directly on the networks concerned.

This reflects a broader doctrinal evolution. Cyber is no longer treated as a static defensive function. It is increasingly understood as an active capability, aimed at identifying threats as close as possible to their point of origin. The United States Department of Defense cyber strategy formalizes this approach by emphasizing forward operations designed to limit the impact of threats on national and allied systems.
Standardized kits make this shift tangible. At the same time, they introduce new constraints, particularly in terms of logistics, sustainment, and deployment cycles.
What is actually inside a deployable cyber kit
The term “cyber kit” is often used loosely, but in practice it refers to a structured combination of hardware and software designed to enable direct intervention on a network, sometimes unfamiliar, in constrained conditions.
The first layer is physical. These kits include hardened equipment, typically carried in rugged cases or compact modules, such as secure laptops, portable servers, and network gear. This allows teams to establish an independent analytical environment without immediately relying on local infrastructure, which is essential when operating on partner networks.
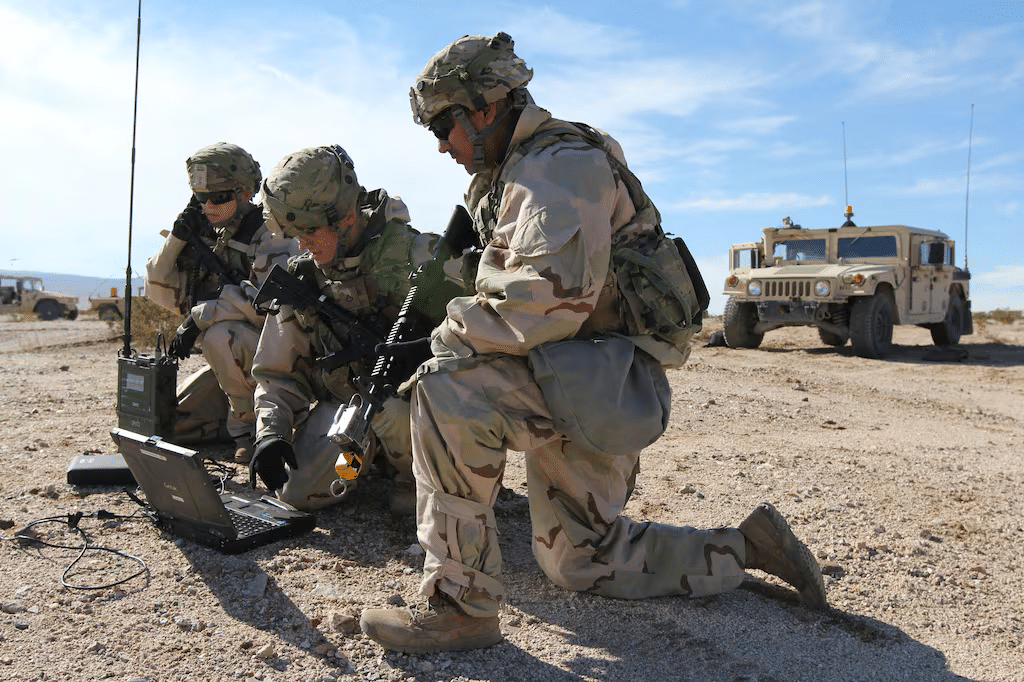
On top of this sits a specialized software stack. The kit carries tools for traffic analysis, anomaly detection, and digital forensics, enabling teams to monitor network activity, flag suspicious behavior, and reconstruct intrusions. This approach aligns directly with forward hunt operations, which focus on actively searching for malicious presence rather than waiting for alerts.
Integration is another critical element. These kits must be able to plug into heterogeneous networks, including legacy systems or poorly documented environments, without disrupting operations. This requires flexible interfaces, passive monitoring capabilities, and rapid network mapping tools.
These systems do not operate in isolation. They depend on continuous data exchange with rear-based analysis centers and on secure communication flows. In practice, this often relies on hybrid networks combining terrestrial infrastructure and satellite systems. As a result, deployable cyber capabilities are directly dependent on the quality and security of these connections.
A cyber kit should therefore not be seen as a standalone tool, but as a mobile extension of a broader defense architecture. It reflects a shift from centralized cyber capabilities to distributed, field-deployed systems directly exposed to operational constraints.
A genuinely expeditionary capability
Calling cyber an expeditionary capability goes beyond simple mobility. It points to a deeper shift: the ability to project teams, tools, and effects into external environments that are often heterogeneous and only partially under control.
Forward presence operations illustrate this clearly. Cyber teams operate directly on foreign networks, within cooperative frameworks, to identify threats before they can propagate.
This approach requires more than deployable equipment. It depends on trained personnel, technical interoperability, and legal frameworks that enable operations on non-national systems.
Cyber is therefore becoming a capability that must be planned, supported, and sustained in the same way as other operational functions, with comparable demands in terms of preparation and continuity.
Increasing dependence on a complex physical chain
As cyber becomes more mobile and more deeply embedded in operations, it depends on a broader and more interconnected technical infrastructure.
Modern networks combine terrestrial and space segments, ground stations, communications links, and distributed digital services, resulting in highly complex hybrid architectures.

This complexity expands the attack surface. Each component of the chain can become a point of vulnerability. Cyber defense is no longer limited to protecting information systems. It now requires securing an entire ecosystem of interdependent physical and digital infrastructures.
Satellite constellations at the center of new vulnerabilities
Satellite constellations, particularly those in low orbit, are becoming central to modern communication architectures, especially for deployed operations. They enable global connectivity, but they also introduce new risks.
A joint guide published in March 2026 highlights several categories of vulnerability, including weaknesses in ground segments, supply chain exposure, and risks affecting communication links.
These issues have direct operational implications. Expeditionary cyber capabilities depend on resilient, secure connectivity. When that connectivity is degraded or compromised, the capability itself is affected.
Cyber can therefore no longer be separated from the security of space systems and the networks that connect them to users.
Cyber defense is entering a more concrete, more visible, and more demanding phase. The spread of deployable kits and the integration of cyber into forward operations reflect a structural transformation. Cyber is becoming a field capability in its own right. At the same time, this evolution increases dependence on complex infrastructures, particularly satellite constellations, which act both as enablers and as sources of vulnerability.
The central question is therefore changing. The issue is no longer simply who has cyber capabilities, but who can project them, sustain them, and secure the full technical chain that makes them possible.





